Download SOA Security Lab.S90.20.Pass4Success.2026-01-25.24q.vcex
| Vendor: | Arcitura Education |
| Exam Code: | S90.20 |
| Exam Name: | SOA Security Lab |
| Date: | Jan 25, 2026 |
| File Size: | 2 MB |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Purchase
Coupon: TAURUSSIM_20OFF
Discount: 20%
Demo Questions
Question 1
Service Consumer A sends a request to Service A (1). Service A replies with an acknowledgement message (2) and then processes the request and sends a request message to Service B (3). This message contains confidential financial data. Service B sends three different request messages together with its security credentials to Services C, D, and E (4, 5, 6). Upon successful authentication, Services C, D, and E store the data from the message in separate databases (7, 8, 9) Services B, C, D, and E belong to Service Inventory A, which further belongs to Organization B .Service Consumer A and Service A belong to Organization A .The service contracts of Services A and B both comply with the same XML schema. However, each organization employs different security technologies for their service architectures. To protect the confidential financial data sent by Service A to Service B, each organization decides to independently apply the Data Confidentiality and the Data Origin Authentication patterns to establish message-layer security for external message exchanges. However, when an encrypted and digitally signed test message is sent by Service A to Service B, Service B was unable to decrypt the message. Which of the following statements describes a solution that solves this problem?
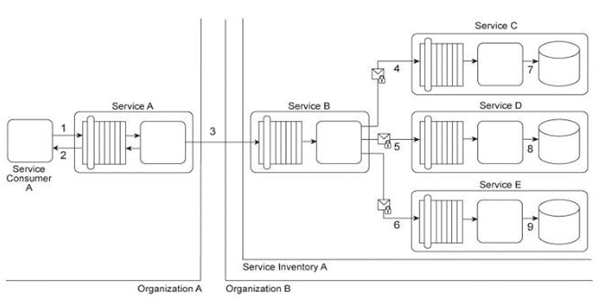
- Although both of the organizations applied the Data Confidentiality and the Data Origin Authentication patterns, the security-technologies used for the Service A and Service B architectures may be incompatible. Because there are several technologies and versions of technologies that can be used to apply these patterns, the organizations need to standardize implementation level details of the relevant security technologies.
- The problem with the test message occurred because Service A used incorrect keys to protect the message sent to Service B .Service A used its own public key to sign the message and then used Service B's public key to encrypt the message content. To correct the problem, Service A must use WS-Secure-Conversation to agree on a secret session key to be used to encrypt messages exchanged between Services A and B .Because this session key is only known by Services A and B, encrypting the messages with this key also provides authentication of the origin of the data.
- Although both of the organizations successfully applied the Data Confidentiality and the Data Origin Authentication patterns, the order in which the patterns were applied is incorrect. The application of the Data Origin Authentication pattern must always follow the application of the Data Confidentiality pattern to ensure that the message confidentiality from a third party authenticates the origin of the message.
- The problem with the test message occurred because Service A needed the private key of Service B to digitally sign the-message. An attacker pretending to be Service B likely sent a fake private/public keys pair to Service A .Using these fake keys to encrypt and digitally sign the message made the message incompatible for Service B .Because the fake private key was also used to sign the hash, it explains the source of the problem.
Correct answer: A
Question 2
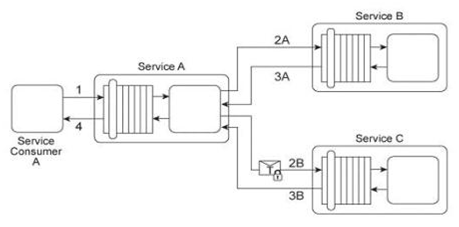
Service A is a publically accessible service that provides free multimedia retrieval capabilities to a range of service consumers. To carry out this functionality, Service A is first invoked by Service Consumer A (1). Based on the nature of the request message received from Service Consumer A, Service A either invokes Service B or Service C .When Service B is invoked by Service A (2A) it retrieves data from publicly available sources (not shown) and responds with the requested data (3A). When Service C is invoked by Service A (2B) it retrieves data from proprietary sources within the IT enterprise (not shown) and responds with the requested data (3B). After receiving a response from Service B or Service C, Service A sends the retrieved data to Service Consumer A (4). Service B does not require service consumers to be authenticated, but Service C does require authentication of service consumers. The service contract for Service A therefore uses WS-Policy alternative policies in order to express the two different authentication requirements to Service Consumer A .When Service Consumer A sends a request message (1), Service A determines whether the request requires the involvement of Service C and then checks to ensure that the necessary security credentials were received as part of the message. If the credentials provided by Service Consumer A are verified. Service A creates a signed SAML assertion and sends it with the request message to Service C (2B) This authentication information is protected by public key encryption However, responses to Service Consumer A's request message (3B, 4) are not encrypted for performance reasons. Recently, the usage of Service C has noticeably declined. An investigation has revealed response messages issued by Service C (3B) have been repeatedly intercepted and accessed by unauthorized and malicious intermediaries. As a result, Service Consumer A has lost confidence in the use of Service A for the retrieval of proprietary data because it is being viewed as a security risk. This is especially troubling, because the owner of Service A had planned to start charging a fee for Service A's ability to provide proprietary data via the use of Service C .How can this service composition architecture be changed to address the security problem with minimal impact on runtime performance?
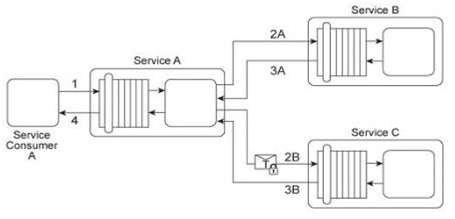
- Use the existing PKI to provide message-layer security for the response messages originating from Service C .To provide-message confidentiality, Service C can encrypt the response messages using Service Consumer A's public key. This prevents unauthorized intermediaries from accessing the content of response messages.
- Use the existing PKI to provide two-way authentication of the exchanged messages. After receiving a request from the service consumer, Service A can respond with a signed acknowledgement of the message, encrypted by the public key of Service Consumer A .Only Service Consumer A will be able to decrypt the encrypted acknowledgement. Service Consumer A then responds to the acknowledgement, thereby verifying its identity with Service A .Because both Service Consumer A and Service A are mutually authenticated, end-to-end transport-layer security is sufficient to provide message confidentiality in order to prevent unauthorized intermediaries from accessing messages originating from Service C .
- Use the existing PKI to establish secure communication between Service Consumer A and Service C .A symmetric key can be generated for the data being sent from Service C to Service Consumer A Service C can generate a session key that is encrypted with Service Consumer A's public key. Service C can then attach the session key to the response message, which is encrypted using the session key. Because only Service Consumer A can decrypt the encrypted session key, the data transmitted in the message is safe from access by unauthorized intermediaries.
- Use the existing PKI to specify encryption and digital signature requirements on the messages. Service C can use Service-Consumer A's public key to generate a symmetric key. Service Consumer A can also generate the same session key from its own public key. Service C can use the session key to encrypt the response message (and the hash value of the response message), concatenate them, and send them to Service Consumer A .Service Consumer A separates the concatenated and encrypted hash value, decrypts it, and then decrypts the encrypted response message. As a result, the confidentiality and integrity of the response message are guaranteed.
Correct answer: C
Question 3
Service A provides a customized report generating capability. Due to infrastructure limitations, the number of service consumers permitted to access Service A concurrently is strictly controlled. Service A validates request messages based on the supplied credentials (1). If the authentication of the request message is successful, Service A sends a message to Service B (2) to retrieve the required data from Database A (3). Service A stores the response from Service B (4) in memory and then issues a request message to Service C (5). Service C retrieves a different set of data from Database A (6) and sends the result back to Service A (7). Service A consolidates the data received from Services B and C and sends the generated report in the response message to the service consumer (8). It has been discovered that attackers have been gaining access to confidential data exchanged between Service A and Service B, and between Service A and its service consumers. What changes can be made to this service composition architecture in order to counter this threat?
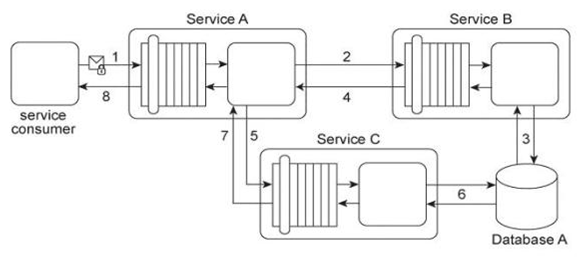
- Apply the Service Perimeter Guard pattern in order to protect message exchanges between Service A and its service-consumers. Apply the Direct Authentication pattern in order to protect message exchanges between Service A and Service B .
- Apply the Direct Authentication pattern in order to protect message exchanges between Service A and its service consumers and between Service A and Service B .This approach will establish a password-based authentication mechanism that relies on a local identity store and will therefore prevent access by attackers.
- Apply the Data Origin Authentication pattern to protect the final report sent by Service A to its service consumer. Service A can generate a message digest of the final report, after which it can sign the digest with its own private key. It then can send both the final report and the signed-message digest to its service consumer. This service consumer can generate its own message digest, decrypt the signed digest using the public key of Service A (which proves that Service A sent the message), and then compare the two digests. If the digests match, it guarantees that the final report was not tampered with during transmission.
- None of the above
Correct answer: D
Question 4
Service A provides a data access capability that can be used by a variety of service consumers. The database records accessed by Service A are classified as either private or public. There are two types of service consumers that use Service A:
Service consumers with public access permissions (allowed to access only public data records) and service consumers with private access permissions (allowed to access all data records). For performance reasons the Service A architecture uses a single database, named Database A .Each record in Database A is classified as either private or public. After Service A is invoked by a service consumer (1), it authenticates the request message using an identity store and retrieves the corresponding authorization (2, 3). Once authorized, the service consumer's request is submitted to Database A (4), which then returns the requested data (5) If the service consumer has private access permissions, all of the returned data is included in Service A's response message (6). If the service consumer has public access permissions, then Service A first filters the data in order to remove all unauthorized private data records, before sending to the response message to the service consumer (6). An investigation recently detected that private data has been leaked to unauthorized service consumers. An audit of the Service A architecture revealed that Service A's filtering logic is flawed, resulting in situations where private data was accidentally shared with service consumers that only have public access permissions. Further, it was discovered that attackers have been monitoring response messages sent by Service A in order to capture private data. It is subsequently decided to split Database A into two databases:
one containing only private data (the Private Database) and the other containing only public data (the Public Database). What additional changes are necessary to address these security problems?
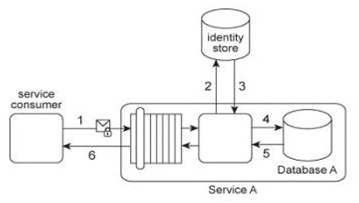
- The Service A logic needs to be modified to work with the two new databases. Service A needs to be able to access the Public Database and the Private Database when it receives a request message from a service consumer with private access permissions, and it must only access the Public Database when it receives a request message from a service consumer with public access permissions. Furthermore, any response messages issued by Service A containing private data need to be encrypted.
- A utility service needs to be created and positioned between Service A and the service consumer. The utility service can-contain screening logic that can verify the service consumer's credentials and then forward the request message to the Private Database or to the Public Database, depending on the service consumer's access permissions. Because each request message is evaluated by the database, no filtering of the returned data is necessary. The data is sent back to the consumer in a response message encrypted using symmetric key encryption.
- After the service consumer's request message is authenticated. Service A can generate a onetime symmetric encryption key that it sends to the service consumer. This key is encrypted by the public key of the service consumer. After the service consumer acknowledges the receipt of the one-time encryption key, Service A forwards the service consumer's data access request (and the corresponding credentials) to both databases. After receiving the responses from the databases, Service A compiles the results into a single response message. This message is encrypted with the one-time key and sent by Service A to the service consumer.
- The Service A architecture can be enhanced with certificate-based authentication of service consumers in order to avoid dependency on the identity store. By using digital certificates, Service A can authenticate a service consumer's request message and then forward the data access request to the appropriate database. After receiving the responses from the databases, Service A can use the service consumer's public key to encrypt the response message that is sent to the service consumer.
Correct answer: A
Question 5
Service Consumer A submits a request message with security credentials to Service A (1). The identity store that Service A needs to use in order to authenticate the security credentials can only be accessed via a legacy system that resides in a different service inventory. Therefore, to authenticate Service Consumer A, Service A must first forward the security credentials to the legacy system (2). The legacy system then returns the requested identity to Service A (3). Service A authenticates Service Consumer A against the identity received from the legacy system. If the authentication is successful, Service A retrieves the requested data from Database A (4), and returns the data in a response message sent back to Service Consumer A (5). Service A belongs to Service Inventory A which further belongs to Security Domain A and the legacy system belongs to Service Inventory B which further belongs to Security Domain B .(The legacy system is encapsulated by other services within Service Inventory B, which are not shown in the diagram.) These two security domains trust each other. Communication between Service A and the legacy system is kept confidential using transport-layer security. No intermediary service agents currently exist between the two service inventories. However, it has been announced that due to the introduction of new systems, some intermediary service agents may be implemented in the near future. Additionally, the legacy system has been scheduled for retirement and will be replaced by a new identity management system that will provide a new identity store. Because the new identity store will need to serve many different systems, there are concerns that it could become a performance bottleneck. As a result, services (including Service A and other services in Security Domains A and B) will not be allowed to directly access the new identity store. Which of the following statements describes a solution that can accommodate the requirements of the new identity store, the authentication requirements of Service A, and can further ensure that message exchanges between Security Domains A and B remain confidential after intermediary service agents are introduced?
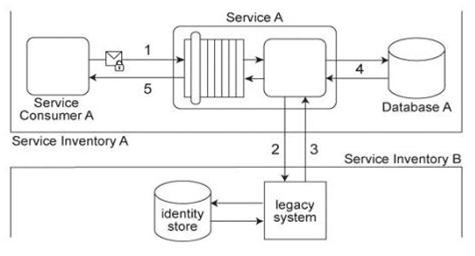
- Apply the Trusted Subsystem pattern to implement a utility service abstracting the new identity management system. Service A forwards Service Consumer As credentials to the utility service to verify Service Consumer As identity. The utility service authenticates the request originating from Service A .After successful authentication, the utility service uses its own credentials to retrieve the requested identity, and then send the identity to Service A, Therefore, effectively reducing the processing need of the identity management system. The current transport-layer security can still be used, in order to secure the communication between Service A and the new utility service, as it more efficient than the message-layer security.
- Apply the Trusted Subsystem pattern by abstracting away the new identity management system using a utility service that authenticates the request from Service A and then uses its own credentials to retrieve the requested identity from the new identity management system. For the utility service to authenticate Service As request, it needs to be provisioned with a new identity database that contains identities for all authorized service consumers of the new utility service. In order to secure the communication between Service A and the new utility service, use message-layer security as it provides security over multiple hops considering the need to secure the message in case an intermediary is introduced in future.
- Replicate the identity database used by the new identity management system. Because the Security Domains A and B trust each other, protection of the identity store is guaranteed. Use Service Agents to monitor changes to the identity database used by the new identity management system and to update the replica. This would satisfy the security needs of Service A, would eliminate the need to request services from Service Inventory B, and ensure that current identity information is available for Service A .Because Service A would not need to access services across different trust domains, the current transport-layer security is sufficient.
- Apply the Brokered Authentication pattern to establish an authentication broker. Instead of Service A directly authenticating-Service Consumer A, Service Consumer A submits a request message with security credentials to the authentication broker, which authenticates Service Consumer A against the new identity store and then issues a SAML token to Service Consumer A that it can use for message exchanges with other services, if necessary. In order to secure cross-service inventory message exchanges, the Data Confidentiality pattern is applied to establish message-layer security.
Correct answer: D
Question 6
Service A exchanges messages with Service B multiple times during the same runtime service activity. Communication between Services A and B has been secured using transport-layer security. With each service request message sent to Service B (1A .IB), Service A includes an X.509 certificate, signed by an external Certificate Authority (CA). Service B validates the certificate by retrieving the public key of the CA (2A .2B) and verifying the digital signature of the X.509 certificate. Service B then performs a certificate revocation check against a separate external CA repository (3A, 3B). No intermediary service agents reside between Service A and Service B .Service B has recently suffered from poor runtime performance plus it has been the victim of an access-oriented attack. As a result, its security architecture must be changed to fulfill the following new requirements:
1. The performance of security-related processing carried out by Service B when communicating with Service A must be improved.
2. All request messages sent from Service A to Service B must be screened to ensure that they do not contain malicious content. Which of the following statements describes a solution that fulfills these requirements?
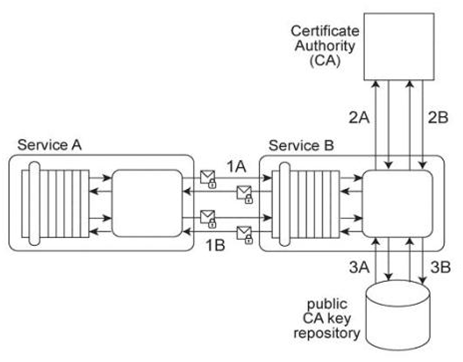
- Eliminate the need to retrieve the public key from the Certificate Authority and to verify the certificate revocation information by extending the service contract of Service B to accept certificates only from pre-registered Certificate Authorities. This form of pre-registration ensures that Service B has the public key of the corresponding Certificate Authority.
- Add a service agent to screen messages sent from Service A to Service B .The service agent can reject any message containing malicious content so that only verified messages are passed through to Service B .Instead of using X.509 certificates, use WS-Secure Conversation sessions. Service A can request a Security Context Token (SCT) from a Security Token Service and use the derived keys from the session key to secure communication with Service B .Service B retrieves the session key from the Security Token Service.
- Apply the Trusted Subsystem pattern by introducing a new utility service between Service A and Service B .When Service A sends request messages, the utility service verifies the provided credentials and creates a customized security profile for Service A .The security profile contains authentication and access control statements that are then inherited by all subsequent request messages issued by Service A .As a result, performance is improved because Service A does not need to resubmit any additional credentials during subsequent message exchanged as part of the same runtime service activity. Furthermore, the utility service performs message screening logic to filter out malicious content.
- Apply the Trusted Subsystem pattern to by introducing a new utility service. Because Service B is required to limit the use of external resources. Service A must ensure that no other services can request processing from Service B in order to prevent malicious content from infiltrating messages. This is achieved by creating a dedicated replica of Service B to be used by the utility service only. Upon receiving the request message and the accompanying security credentials from Service A .the utility service verifies the authentication information and the validity of the X.509 signature. If the authentication information is correct, then the utility service replicates the code of Service B, performs the necessary processing, and returns the response to Service A .
Correct answer: B
Question 7
Service Consumer A sends a request message to Service A (1), after which Service A sends a request message to Service B (2). Service B forwards the message to have its contents calculated by Service C (3). After receiving the results of the calculations via a response message from Service C (4), Service B then requests additional data by sending a request message to Service D (5). Service D retrieves the necessary data from Database A (6), formats it into an XML document, and sends the response message containing the XML-formatted data to Service B (7). Service B appends this XML document with the calculation results received from Service C, and then records the entire contents of the XML document into Database B (8). Finally, Service B sends a response message to Service A (9) and Service A sends a response message to Service Consumer A (10). Services A, B and D are agnostic services that belong to Organization A and are also being reused in other service compositions. Service C is a publicly accessible calculation service that resides outside of the organizational boundary. Database A is a shared database used by other systems within Organization A and Database B is dedicated to exclusive access by Service B .Recently, Service D received request messages containing improperly formatted database retrieval requests. All of these request messages contained data that originated from Service C .There is a strong suspicion that an attacker from outside of the organization has been attempting to carry out SOL injection attacks. Furthermore, it has been decided that each service that writes data to a database must keep a separate log file that records a timestamp of each database record change. Because of a data privacy disclosure requirement used by Organization A, the service contracts of these services need to indicate that this logging activity may occur. How can the service composition architecture be improved to avoid SQL injection attacks originating from Service C - and - how can the data privacy disclosure requirement be fulfilled?
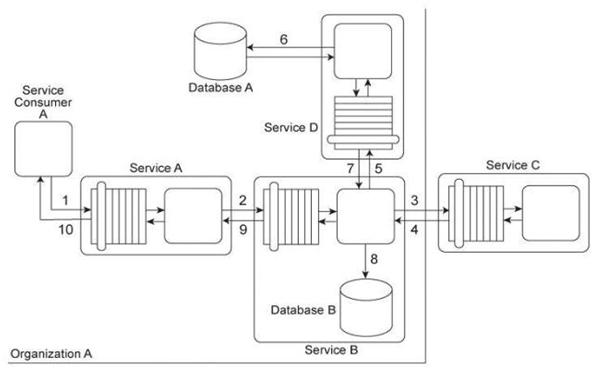
- Apply the Service Perimeter Guard pattern together with the Message Screening pattern in order to establish a perimeter service with message screening logic. Position the perimeter service between Service C and Service B .The message screening logic rejects or filters out potentially harmful content in messages sent from Service C, prior to being forwarded to Service B .Secondly, update the service contracts for Services B and D with an optional WS-Policy assertion that provides service consumers with the option of complying to the logging requirements.
- Apply the Data Origin Authentication pattern to authenticate data received from Service C .Service C digitally signs any datasent in response messages to Service B .Service B can then verify that the data has not been modified during transit and that it originated from Service C .Secondly, update the service contracts for Services B and D with an ignorable WS-Policy assertion that communicates the possibility of the logging activity.
- Apply the Data Origin Authentication pattern to authenticate data received from Service C .Service C digitally signs any datasent in response messages to Service B .Service B can then verify that the data has not been modified during transit and that it originated from Service C .Secondly, update the service contracts for Services B and D with an ignorable WS-Policy assertion that communicates the possibility of the logging activity. The service contracts for Services B and D are updated with an optional WS-Policy assertion that provides service consumers with the option of complying to the logging requirements.
- Apply the Message Screening pattern in order to establish a service agent with message screening logic. Position the service agent between Service C and Service B .The service agent's message screening logic can reject or filter out potentially harmful content in messages sent from Service C, before being processed by Service B .Secondly, update the service contracts for Services B and D with an ignorable WS-Policy assertion that communicates the possibility of the logging activity.
Correct answer: D
Question 8
Service A is a publically accessible service that provides free multimedia retrieval capabilities to a range of service consumers. To carry out this functionality, Service A is first invoked by Service Consumer A (1). Based on the nature of the request message received from Service Consumer A, Service A either invokes Service B or Service C .When Service B is invoked by Service A (2A) it retrieves data from publicly available sources (not shown) and responds with the requested data (3A). When Service C is invoked by Service A (2B) it retrieves data from proprietary sources within the IT enterprise (not shown) and responds with the requested data (3B). After receiving a response from Service B or Service C, Service A sends the retrieved data to Service Consumer A (4). Service B does not require service consumers to be authenticated, but Service C does require authentication of service consumers. The service contract for Service A therefore uses WS-Policy alternative policies in order to express the two different authentication requirements to Service Consumer A .When Service Consumer A sends a request message (1), Service A determines whether the request requires the involvement of Service C and then checks to ensure that the necessary security credentials were received as part of the message. If the credentials provided by Service Consumer A are verified. Service A creates a signed SAML assertion and sends it with the request message to Service C (2B) This authentication information is protected by public key encryption However, responses to Service Consumer A's request message (3B, 4) are not encrypted for performance reasons. The owner of Service C is planning two changes to the service architecture:
1. A fee will be charged to Service Consumer A (or any service consumer) using Service C .2. The response messages issued by Service C need to be secured in order to prevent unauthorized access. An analysis of Service C's usage statistics reveals that a group of service consumers specifically request the retrieval of multimedia data on a frequent basis. To promote the usage of Service C to these types of service consumers, the owner of Service C plans to offer a special discount by allowing unlimited multimedia retrievals for a fixed monthly price. Service consumers that do not subscribe to this promotion will need to pay for each request individually. It is anticipated that the new promotion will significantly increase the usage of Service C .The owner of Service C therefore wants to ensure that the security added to the response messages has a minimal impact on Service C's runtime performance. What steps can be taken to fulfill these requirements?
- Use symmetric session keys so that for each response message, Service C generates a session key and encrypts the-response message using this session key. The session key is then encrypted (using the service consumer's public key) and attached to the encrypted response. A single session key can then be used by Service C for communication with all service consumers that subscribe to the promotion.
- Because the services in this service composition already rely on public key encryption to provide authentication, Service C can provide message confidentiality by encrypting the response message with Service Consumer A's public key. This will ensure that only the intended recipient, in possession of the corresponding private key, can decrypt the response message. To further reduce the performance impact of encryption, Service C can generate a new public-private key pair to be used by service consumers subscribed to the promotion. By securely distributing the private key to each of these service consumers, Service C only needs to encrypt the response messages once with the public key.
- Design Service C to generate a message digest of the response message and encrypt it with the service consumer's publickey. Because the message digest is typically small, the performance of public key encryption is acceptable. This approach also ensures that only the service consumer can decrypt the response message using the corresponding private key.
- Design the service composition architecture so that the encryption of the response messages is performed by Service B and Service C .To reduce the performance impact, a policy can be added to Service A's service contract in order to require the encryption of all response messages, regardless of the type of service consumer making the request. Further, a new utility service can be added to the service composition. This service can be responsible for obtaining the public key of the service consumer and forwarding the key along with the request message to the appropriate service (Service B or Service C). The service receiving the message can then encrypt the response message with the received public key. Service A can then forward the encrypted response to the service consumer. This approach ensures that only authorized service consumers will be able to access response messages.
Correct answer: A
Question 9
Service Consumer A sends a request message to Service A (1) after which Service A retrieves financial data from Database A (2). Service A then sends a request message with the retrieved data to Service B (3). Service B exchanges messages with Service C (4) and Service D (5), which perform a series of calculations on the data and return the results to Service A .Service A uses these results to update Database A (7) and finally sends a response message to Service Consumer A (8). Component B has direct, independent access to Database A and is fully trusted by Database A .Both Component B and Database A reside within Organization A .Service Consumer A and Services A, B, C, and D are external to the organizational boundary of Organization A .
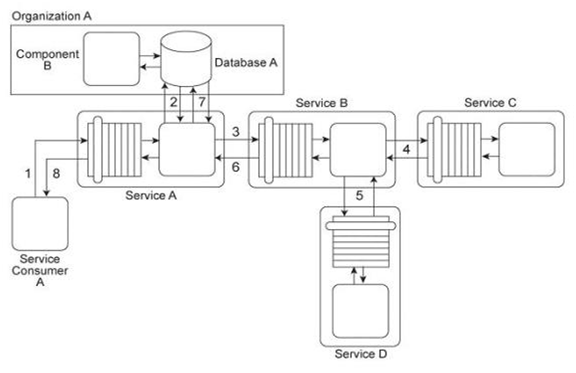
Component B is considered a mission critical program that requires guaranteed access to and fast response from Database A .Service A was recently the victim of a denial of service attack, which resulted in Database A becoming unavailable for extended periods of time (which further compromised Component B). Additionally, Services B, C, and D have repeatedly been victims of malicious intermediary attacks, which have further destabilized the performance of Service A .How can this architecture be improved to prevent these attacks?
- A utility service is created to encapsulate Database A and to assume responsibility for authenticating all access to the database by Service A and any other service consumers. Due to the mission critical requirements of Component B, the utility service further contains logic that strictly limits the amount of concurrent requests made to Database A from outside the organizational boundary. The Data Confidentiality and Data Origin Authentication patterns are applied to all message exchanged within the external service composition in order to establish message-layer security.
- Service Consumer A generates a private/public key pair and sends this public key and identity information to Service A .Service A generates its own private/public key pair and sends it back to Service Consumer A .Service Consumer A uses the public key of Service A to encrypt a randomly generated session key and then sign the encrypted session key with the private key. The encrypted, signed session key is sent to Service A .Now, this session key can be used for secure message-layer communication between Service Consumer A and Service A .The Service Perimeter Guard pattern is applied to establish a perimeter service that encapsulates Database A in order to authenticate all external access requests.
- Services B, C, and D randomly generate Session Key K, and use this key to encrypt request and response messages with symmetric encryption. Session Key K is further encrypted itself asymmetrically. When each service acts as a service consumer by invoking another service, it decrypts the encrypted Session Key K and the invoked service uses the key to decrypt the encrypted response. Database A is replicated so that only the replicated version of the database can be accessed by Service A and other external service consumers.
- The Direct Authentication pattern is applied so that when Service Consumer A submits security credentials, Service A will be able to evaluate the credentials in order to authenticate the request message. If the request message is permitted, Service A invokes the other services and accesses Database A .Database A is replicated so that only the replicated version of the database can be accessed by Service A and other external service consumers.
Correct answer: A
Question 10
Service Consumer A sends a request message with a Username token to Service A (1). Service B authenticates the request by verifying the security credentials from the Username token with a shared identity store (2). To process Service Consumer A's request message, Service A must use Services B, C, and D .Each of these three services also requires the Username token (3. 6, 9) in order to authenticate Service Consumer A by using the same shared identity store (4, 7, 10). Upon each successful authentication, each of the three services (B, C, and D) issues a response message back to Service A (5, 8, 11). Upon receiving and processing the data in all three response messages, Service A sends its own response message to Service Consumer A (12). You are asked to redesign this service composition architecture so that it can still carry out the described message exchanges while requiring that Service Consumer A only be authenticated once using the identity store. Which of the following statements describes an accurate solution?
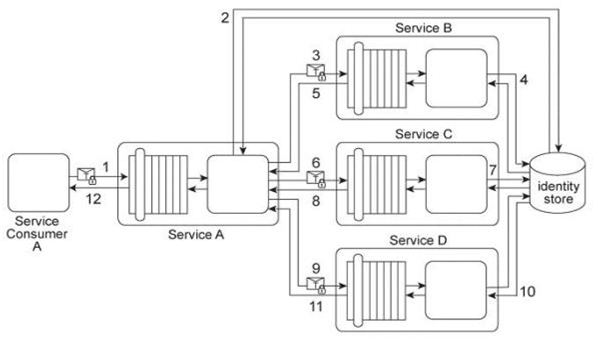
- A single sign-on mechanism is implemented. The Brokered Authentication pattern is applied, resulting in Service A becoming the authentication broker. The authentication broker authenticates the security credentials received from Service Consumer A against the identity store. After successful authentication, the authentication broker issues a signed SAML token for Service Consumer A .The SAML token is subsequently provided to Services B.C .and D by Service A, on behalf of Service Consumer A .
- A single sign-on mechanism is implemented. The Brokered Authentication pattern is applied together with the Data Origin-Authentication pattern. A separate authentication broker utility service is added in between Service Consumer A and Service A .This requires that Service A send its Username token only once to Service B .Service B then acts as a secondary authentication broker and authenticates Service Consumer A and Service A using the identity store. If the authentication is successful,Service B generates a shared secret key to be used as a session key during communication with Services C and D .Because the session key is only known by these services, it can be used authenticates the services to each other.
- A single sign-on mechanism is implemented. The Brokered Authentication pattern is applied together with the Data Origin Authentication pattern. Service A is redesigned to use holder-of-key based subject confirmation SAML assertions. This way, Service A only needs to send its Username token once to Service B .Service B then acts as the authentication broker by issuing a SAML token to Service A and then further sends the SAML token to Services C and D on behalf of Service Consumer A and Service A .Service B signs the SAML assertion in order to ensure its authenticity and integrity during message exchanges with Services C and D .
- The Direct Authentication pattern is applied together with an authentication process that uses digital certificates and digital signatures instead of Username tokens. The digital certificate of Service Consumer A is attached to all subsequent request messages issued by Services A, B, C and D and these request messages are further signed by a private key.
Correct answer: A
Question 11
Services A, B and C belong to Service Inventory A .Services D, E and F belong to Service Inventory B .Service C acts as an authentication broker for Service Inventory A .Service F acts as an authentication broker for Service Inventory B .Both of the authentication brokers use Kerberos-based authentication technologies. Upon receiving a request message from a service consumer, Services C and F authenticate the request using a local identity store and then use a separate Ticket Granting Service (not shown) to issue the Kerberos ticket to the service consumer. A recent security audit of the two service inventories revealed that both authentication brokers have been victims of attacks. In Service Inventory A, the attacker has been intercepting and modifying the credential information sent by Service C (the ticket requester) to the Ticket Granting Service. As a result, the requests have been invalidated and incorrectly rejected by the Ticket Granting Service. In Service Inventory B, the attacker has been obtaining service consumer credentials and has used them to request and receive valid tickets from the Ticket Granting Service. The attacker has then used these tickets to enable malicious service consumers to gain access to other services within the service inventory. How can the two service inventory security architectures be improved in order to counter these attacks?
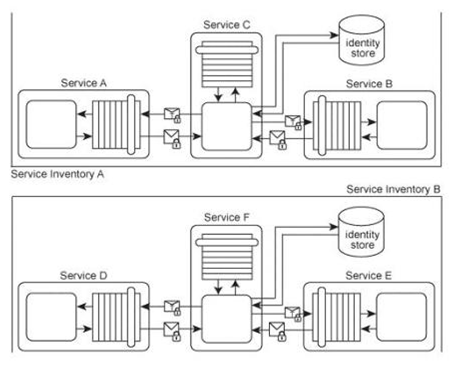
- The Data Confidentiality pattern can be applied to messages exchanged by the services in Service Inventory A .The Data Origin Authentication pattern can be applied to messages exchanged by services in Service Inventory B .
- The Service Perimeter Guard pattern can be applied to Service Inventory A in order to establish a perimeter service responsible for validating and filtering all incoming request messages on behalf of Service C .The Data Origin Authentication pattern can be applied to messages exchanged by services in Service Inventory B .This will ensure the integrity of messages by verifying their origins to the message recipients.
- WS-Secure-Conversation can be used to secure the communication between the authentication broker and service consumers in Service Inventory A .This ensures that Services A and B will contact Service C to request a security context token that will be used to generates a session key for the encryption of the ticket submitted to Service C . The Data Origin Authentication pattern can be applied to messages exchanged by services in Service Inventory B .This will ensure the integrity of messages try verifying their origins to the message recipients.
- WS-Trust can be used to establish secure communication between the authentication broker and the service consumers. After receiving the request message and the corresponding credentials from service consumers, the authentication broker can validate their identity, and if successful, a signed SAML assertion containing all authentication information will be issued. The SAML assertion will then be used to authenticate the service consumers during subsequent communications. Because the messages are signed and encrypted, malicious service consumers cannot access the data. This approach can be applied to counter the threats in both Service Inventories A and B .
Correct answer: A
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX FILES
Use ProfExam Simulator to open VCEX files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



