Download Implementing and Operating Cisco Security Core Technologies.350-701.Pass4Success.2026-05-12.123q.vcex
| Vendor: | Cisco |
| Exam Code: | 350-701 |
| Exam Name: | Implementing and Operating Cisco Security Core Technologies |
| Date: | May 12, 2026 |
| File Size: | 1 MB |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Purchase
Coupon: TAURUSSIM_20OFF
Discount: 20%
Demo Questions
Question 1
[Network Security]
An engineer is configuring 802.1X authentication on Cisco switches in the network and is using CoA as a mechanism. Which port on the firewall must be opened to allow the CoA traffic to traverse the network?
- TCP 6514
- UDP 1700
- TCP 49
- UDP 1812
Correct answer: B
Explanation:
CoA Messages are sent on two different udp ports depending on the platform. Cisco standardizes on UDP port 1700, while the actual RFC calls out using UDP port 3799. CoA Messages are sent on two different udp ports depending on the platform. Cisco standardizes on UDP port 1700, while the actual RFC calls out using UDP port 3799.
Question 2
[Endpoint Protection and Detection]
What is the purpose of the Cisco Endpoint loC feature?
- It provides stealth threat prevention.
- lt is a signature-based engine.
- lt is an incident response tool
- It provides precompromise detection.
Correct answer: C
Explanation:
https://www.cisco.com/c/dam/en_us/about/doing_business/legal/service_descriptions/docs/Cisco_Secure_Managed_Endpoint.pdf https://www.cisco.com/c/dam/en_us/about/doing_business/legal/service_descriptions/docs/Cisco_Secure_Managed_Endpoint.pdf
Question 3
[Security Concepts]
Which telemetry data captures variations seen within the flow, such as the packets TTL, IP/TCP flags, and payload length?
- interpacket variation
- software package variation
- flow insight variation
- process details variation
Correct answer: A
Explanation:
The telemetry information consists of three types of data:+ Flow information: This information contains details about endpoints, protocols, ports, when the flow started, how long the flow was active, etc.+ Interpacket variation: This information captures any interpacket variations within the flow. Examples include variation in Time To Live (TTL), IP and TCP flags, payload length, etc+ Context details: Context information is derived outside the packet header. It includes details about variation in buffer utilization, packet drops within a flow, association with tunnel endpoints, etc. The telemetry information consists of three types of data:
+ Flow information: This information contains details about endpoints, protocols, ports, when the flow started, how long the flow was active, etc.
+ Interpacket variation: This information captures any interpacket variations within the flow. Examples include variation in Time To Live (TTL), IP and TCP flags, payload length, etc
+ Context details: Context information is derived outside the packet header. It includes details about variation in buffer utilization, packet drops within a flow, association with tunnel endpoints, etc.
Question 4
[Security Concepts]
What is the main role of the Cisco Email Security Appliance?
- Mail Submission Agent
- Mail Transfer Agent
- Mail Delivery Agent
- Mail User Agent
Correct answer: B
Explanation:
Cisco Email Security Appliance (ESA) protects the email infrastructure and employees who use email at work by filtering unsolicited and malicious email before it reaches the user. Cisco ESA easily integrates into existing email infrastructures with a high degree of flexibility. It does this by acting as a Mail Transfer Agent (MTA) within the email-delivery chain. Another name for an MTA is a mail relay. Cisco Email Security Appliance (ESA) protects the email infrastructure and employees who use email at work by filtering unsolicited and malicious email before it reaches the user. Cisco ESA easily integrates into existing email infrastructures with a high degree of flexibility. It does this by acting as a Mail Transfer Agent (MTA) within the email-delivery chain. Another name for an MTA is a mail relay.
Question 5
[Security Concepts]
An organization wants to implement a cloud-delivered and SaaS-based solution to provide visibility and threat detection across the AWS network. The solution must be deployed without software agents and rely on AWS VPC flow logs instead. Which solution meets these requirements?
- Cisco Stealthwatch Cloud
- Cisco Umbrella
- NetFlow collectors
- Cisco Cloudlock
Correct answer: A
Explanation:
Cisco Stealthwatch Cloud is a cloud-delivered and SaaS-based solution that provides visibility and threat detection across the AWS network. It does not require any software agents to be installed on the AWS instances, and it relies on AWS VPC flow logs to collect network traffic metadata. Cisco Stealthwatch Cloud analyzes the flow logs using machine learning and behavioral modeling to detect anomalies and threats, such as data exfiltration, lateral movement, reconnaissance, and compromised instances. Cisco Stealthwatch Cloud also provides contextual information and actionable alerts to help users respond to incidents and remediate issues.Cisco Umbrella is a cloud-delivered and SaaS-based solution that provides DNS-layer security and web filtering for internet traffic. It does not provide visibility and threat detection for internal AWS network traffic, and it requires software agents to be installed on the endpoints or network devices to enforce policies and redirect DNS requests.NetFlow collectors are devices or software applications that collect and analyze NetFlow records, which are generated by network devices to capture information about IP traffic flows. NetFlow collectors can provide visibility and threat detection for network traffic, but they are not cloud-delivered or SaaS-based solutions. They also require NetFlow exporters to be configured on the network devices, which may not be supported by AWS.Cisco Cloudlock is a cloud-delivered and SaaS-based solution that provides cloud security posture management (CSPM) and cloud access security broker (CASB) capabilities for cloud applications and environments. It does not provide visibility and threat detection for AWS network traffic, and it does not rely on AWS VPC flow logs. It focuses on protecting cloud data, users, and configurations from misconfigurations, compliance violations, and malicious activities.Reference:=Cisco Stealthwatch Cloud for AWSCisco UmbrellaNetFlow[Cisco Cloudlock] Cisco Stealthwatch Cloud is a cloud-delivered and SaaS-based solution that provides visibility and threat detection across the AWS network. It does not require any software agents to be installed on the AWS instances, and it relies on AWS VPC flow logs to collect network traffic metadata. Cisco Stealthwatch Cloud analyzes the flow logs using machine learning and behavioral modeling to detect anomalies and threats, such as data exfiltration, lateral movement, reconnaissance, and compromised instances. Cisco Stealthwatch Cloud also provides contextual information and actionable alerts to help users respond to incidents and remediate issues.
Cisco Umbrella is a cloud-delivered and SaaS-based solution that provides DNS-layer security and web filtering for internet traffic. It does not provide visibility and threat detection for internal AWS network traffic, and it requires software agents to be installed on the endpoints or network devices to enforce policies and redirect DNS requests.
NetFlow collectors are devices or software applications that collect and analyze NetFlow records, which are generated by network devices to capture information about IP traffic flows. NetFlow collectors can provide visibility and threat detection for network traffic, but they are not cloud-delivered or SaaS-based solutions. They also require NetFlow exporters to be configured on the network devices, which may not be supported by AWS.
Cisco Cloudlock is a cloud-delivered and SaaS-based solution that provides cloud security posture management (CSPM) and cloud access security broker (CASB) capabilities for cloud applications and environments. It does not provide visibility and threat detection for AWS network traffic, and it does not rely on AWS VPC flow logs. It focuses on protecting cloud data, users, and configurations from misconfigurations, compliance violations, and malicious activities.Reference:=
Cisco Stealthwatch Cloud for AWS
Cisco Umbrella
NetFlow
[Cisco Cloudlock]
Question 6
[Security Concepts]
A Cisco Firepower administrator needs to configure a rule to allow a new application that has never been seen on the network. Which two actions should be selected to allow the traffic to pass without inspection? (Choose two)
- permit
- trust
- reset
- allow
- monitor
Correct answer: B, E
Explanation:
Each rule also has an action, which determines whether you monitor, trust, block, or allow matching traffic.Note: With action ''trust'', Firepower does not do any more inspection on the traffic. There will be no intrusion protection and also no file-policy on this traffic. Each rule also has an action, which determines whether you monitor, trust, block, or allow matching traffic.
Note: With action ''trust'', Firepower does not do any more inspection on the traffic. There will be no intrusion protection and also no file-policy on this traffic.
Question 7
[Endpoint Protection and Detection]
What is a required prerequisite to enable malware file scanning for the Secure Internet Gateway?
- Enable IP Layer enforcement.
- Activate the Advanced Malware Protection license
- Activate SSL decryption.
- Enable Intelligent Proxy.
Correct answer: D
Explanation:
To enable malware file scanning for the Secure Internet Gateway (SIG), you need to enable Intelligent Proxy, which is a feature of Cisco Umbrella that provides selective proxying of web requests based on the risk level of the domain1.Intelligent Proxy allows SIG to inspect the content of potentially malicious web requests and block or allow them based on the configured policies2.Intelligent Proxy also enables SSL decryption, which is necessary to scan encrypted web traffic for malware3.Enabling IP Layer enforcement, activating the Advanced Malware Protection license, and activating SSL decryption are not required prerequisites to enable malware file scanning for the SIG, although they may provide additional security benefits45.Reference:1:Intelligent Proxy - Cisco Umbrella2:Cisco Umbrella SIG Advantage - Cisco Umbrella3:[SSL Decryption - Cisco Umbrella]4:[IP Layer Enforcement - Cisco Umbrella]5:[Advanced Malware Protection - Cisco Umbrella] To enable malware file scanning for the Secure Internet Gateway (SIG), you need to enable Intelligent Proxy, which is a feature of Cisco Umbrella that provides selective proxying of web requests based on the risk level of the domain1.Intelligent Proxy allows SIG to inspect the content of potentially malicious web requests and block or allow them based on the configured policies2.Intelligent Proxy also enables SSL decryption, which is necessary to scan encrypted web traffic for malware3.Enabling IP Layer enforcement, activating the Advanced Malware Protection license, and activating SSL decryption are not required prerequisites to enable malware file scanning for the SIG, although they may provide additional security benefits45.Reference:1:Intelligent Proxy - Cisco Umbrella2:Cisco Umbrella SIG Advantage - Cisco Umbrella3:
[SSL Decryption - Cisco Umbrella]4:
[IP Layer Enforcement - Cisco Umbrella]5:
[Advanced Malware Protection - Cisco Umbrella]
Question 8
[Network Security]
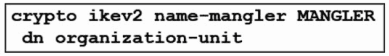
Refer to the exhibit. An engineer is implementing a certificate-based VPN. What is the result of the existing configuration?
- The OU of the IKEv2 peer certificate is encrypted when the OU is set to MANGLER.
- The OU of the IKEv2 peer certificate is used as the identity when matching an IKEv2 authorization policy.
- Only an IKEv2 peer that has an OU certificate attribute set to MANGLER establishes an IKEv2 SA successfully.
- The OU of the IKEv2 peer certificate is set to MANGLER.
Correct answer: C
Question 9
[Endpoint Protection and Detection]
An engineer is configuring AMP for endpoints and wants to block certain files from executing. Which outbreak control method is used to accomplish this task?
- device flow correlation
- simple detections
- application blocking list
- advanced custom detections
Correct answer: C
Explanation:
The application blocking list is an outbreak control method that allows the administrator to block certain files from executing on the endpoints based on their SHA values. This can prevent malware from running on the endpoints and causing damage. The other options are not outbreak control methods, but rather different features of AMP for endpoints. Device flow correlation is a network analysis feature that monitors connections and detects malicious activity. Simple detections and advanced custom detections are custom rules that can be created by the administrator to detect and block files based on signatures or other criteria.Reference:Configure Windows Policy in AMP for Endpoints - CiscoPrevent, Detect and Respond with Cisco AMP for Endpoints The application blocking list is an outbreak control method that allows the administrator to block certain files from executing on the endpoints based on their SHA values. This can prevent malware from running on the endpoints and causing damage. The other options are not outbreak control methods, but rather different features of AMP for endpoints. Device flow correlation is a network analysis feature that monitors connections and detects malicious activity. Simple detections and advanced custom detections are custom rules that can be created by the administrator to detect and block files based on signatures or other criteria.Reference:
Configure Windows Policy in AMP for Endpoints - Cisco
Prevent, Detect and Respond with Cisco AMP for Endpoints
Question 10
[Endpoint Protection and Detection]
Which security solution is used for posture assessment of the endpoints in a BYOD solution?
- Cisco FTD
- Cisco ASA
- Cisco Umbrella
- Cisco ISE
Correct answer: D
Explanation:
Cisco ISE is the security solution that is used for posture assessment of the endpoints in a BYOD solution. Posture assessment allows Cisco ISE to inspect the security health of the endpoints, such as their operating system, software applications, network settings, and security software. Cisco ISE can then enforce posture policies based on the compliance status of the endpoints and grant or deny them access to the network resources. Cisco ISE supports different types of posture agents, such as AnyConnect, AnyConnect Stealth, and Temporal Agent, to monitor and remediate the endpoints. Cisco ISE also supports agentless posture for devices that cannot run an agent, such as printers, cameras, and IoT devices. Cisco ISE integrates with various third-party vendors to provide posture assessment for different endpoint platforms, such as Windows, Mac, Linux, Android, and iOS.Reference:=Some possible references are:Cisco Identity Services Engine Administrator Guide, Release 3.0 - ComplianceChapter 15. Device Posture Assessment - Cisco ISE for BYOD and Secure Unified AccessImplementing and Operating Cisco Security Core Technologies (SCOR) v1.0 Cisco ISE is the security solution that is used for posture assessment of the endpoints in a BYOD solution. Posture assessment allows Cisco ISE to inspect the security health of the endpoints, such as their operating system, software applications, network settings, and security software. Cisco ISE can then enforce posture policies based on the compliance status of the endpoints and grant or deny them access to the network resources. Cisco ISE supports different types of posture agents, such as AnyConnect, AnyConnect Stealth, and Temporal Agent, to monitor and remediate the endpoints. Cisco ISE also supports agentless posture for devices that cannot run an agent, such as printers, cameras, and IoT devices. Cisco ISE integrates with various third-party vendors to provide posture assessment for different endpoint platforms, such as Windows, Mac, Linux, Android, and iOS.Reference:=
Some possible references are:
Cisco Identity Services Engine Administrator Guide, Release 3.0 - Compliance
Chapter 15. Device Posture Assessment - Cisco ISE for BYOD and Secure Unified Access
Implementing and Operating Cisco Security Core Technologies (SCOR) v1.0
Question 11
[Network Security]
What is a difference between a zone-based firewall and a Cisco Adaptive Security Appliance firewall?
- Zone-based firewalls provide static routing based on interfaces, and Cisco Adaptive Security Appliance firewalls provide dynamic routing.
- Zone-based firewalls support virtual tunnel interfaces across different locations, and Cisco Adaptive Security Appliance firewalls support DMVPN.
- Zone-based firewalls have a default allow-all policy between interfaces in the same zone, and Cisco Adaptive Security Appliance firewalls have a deny-all policy.
- Zone-based firewalls are used in large deployments with multiple areas, and Cisco Adaptive Security Appliance firewalls are used in small deployments.
Correct answer: C
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX FILES
Use ProfExam Simulator to open VCEX files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



