Download CompTIA CSA+.CS0-003.ExamTopics.2025-10-03.458q.vcex
| Vendor: | CompTIA |
| Exam Code: | CS0-003 |
| Exam Name: | CompTIA CSA+ |
| Date: | Oct 03, 2025 |
| File Size: | 12 MB |
How to open VCEX files?
Files with VCEX extension can be opened by ProfExam Simulator.
Purchase
Coupon: TAURUSSIM_20OFF
Discount: 20%
Demo Questions
Question 1
The Chief Executive Officer of an organization recently heard that exploitation of new attacks in the industry was happening approximately 45 days after a patch was released. Which of the following would best protect this organization?
- A mean time to remediate of 30 days
- A mean time to detect of 45 days
- A mean time to respond of 15 days
- Third-party application testing
Correct answer: A
Explanation:
A: 48 - MostedC: 8 A: 48 - MostedC: 8
Question 2
A recent zero-day vulnerability is being actively exploited, requires no user interaction or privilege escalation, and has a significant impact to confidentiality and integrity but not to availability. Which of the following CVE metrics would be most accurate for this zero-day threat?
- CVSS:31/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:K/A:L
- CVSS:31/AV:K/AC:L/PR:H/UI:R/S:C/C:H/I:H/A:L
- CVSS:31/AV:N/AC:L/PR:N/UI:H/S:U/C:L/I:N/A:H
- CVSS:31/AV:L/AC:L/PR:R/UI:R/S:U/C:H/I:L/A:H
Correct answer: A
Explanation:
A: 35 - MostedB: 2 A: 35 - MostedB: 2
Question 3
Which of the following tools would work best to prevent the exposure of PII outside of an organization?
- PAM
- IDS
- PKI
- DLP
Correct answer: D
Explanation:
D: 8 - Mosted D: 8 - Mosted
Question 4
Which of the following items should be included in a vulnerability scan report? (Choose two.)
- Lessons learned
- Service-level agreement
- Playbook
- Affected hosts
- Risk score
- Education plan
Correct answer: DE
Explanation:
DE: 10 - Mosted DE: 10 - Mosted
Question 5
A security analyst recently joined the team and is trying to determine which scripting language is being used in a production script to determine if it is malicious. Given the following script:
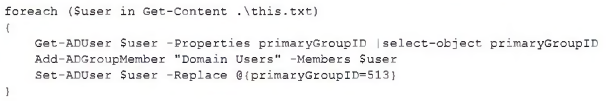
Which of the following scripting languages was used in the script?
- PowerShell
- Ruby
- Python
- Shell script
Correct answer: A
Explanation:
A: 37 - Mosted A: 37 - Mosted
Question 6
A company's user accounts have been compromised. Users are also reporting that the company's internal portal is sometimes only accessible through HTTP, other times; it is accessible through HTTPS. Which of the following most likely describes the observed activity?
- There is an issue with the SSL certificate causing port 443 to become unavailable for HTTPS access
- An on-path attack is being performed by someone with internal access that forces users into port 80
- The web server cannot handle an increasing amount of HTTPS requests so it forwards users to port 80
- An error was caused by BGP due to new rules applied over the company's internal routers
Correct answer: B
Explanation:
B: 32 - Mosted B: 32 - Mosted
Question 7
A security analyst is tasked with prioritizing vulnerabilities for remediation. The relevant company security policies are shown below:
Security Policy 1006: Vulnerability Management
- The Company shall use the CVSSv3.1 Base Score Metrics (Exploitability and Impact) to prioritize the remediation of security vulnerabilities.
- In situations where a choice must be made between confidentiality and availability, the Company shall prioritize confidentiality of data over availability of systems and data.
- The Company shall prioritize patching of publicly available systems and services over patching of internally available system.
According to the security policy, which of the following vulnerabilities should be the highest priority to patch?
- Name: THOR.HAMMER -CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:HInternal System
- Name: CAP.SHIELD -CVSS 3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:NExternal System
- Name: LOKI.DAGGER -CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:HExternal System
- Name: THANOS.GAUNTLET -CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:NInternal System
Correct answer: B
Explanation:
B: 20 - MostedC: 2 B: 20 - MostedC: 2
Question 8
A security analyst received a malicious binary file to analyze. Which of the following is the best technique to perform the analysis?
- Code analysis
- Static analysis
- Reverse engineering
- Fuzzing
Correct answer: C
Explanation:
B: 26C: 41 - Mosted B: 26C: 41 - Mosted
Question 9
A user downloads software that contains malware onto a computer that eventually infects numerous other systems. Which of the following has the user become?
- Hacktivist
- Advanced persistent threat
- Insider threat
- Script kiddie
Correct answer: C
Explanation:
C: 36 - MostedD: 2 C: 36 - MostedD: 2
Question 10
During an extended holiday break, a company suffered a security incident. This information was properly relayed to appropriate personnel in a timely manner and the server was up to date and configured with appropriate auditing and logging. The Chief Information Security Officer wants to find out precisely what happened. Which of the following actions should the analyst take first?
- Clone the virtual server for forensic analysis
- Log m to the affected server and begin analysis of the logs
- Restore from the last known-good backup to confirm there was no loss of connectivity
- Shut down the affected server immediately
Correct answer: A
Explanation:
A: 61 - MostedB: 7C: 1 A: 61 - MostedB: 7C: 1
Question 11
Which of the following will most likely ensure that mission-critical services are available in the event of an incident?
- Business continuity plan
- Vulnerability management plan
- Disaster recovery plan
- Asset management plan
Correct answer: A
Explanation:
A: 53 - MostedB: 1C: 16 A: 53 - MostedB: 1C: 16
HOW TO OPEN VCE FILES
Use VCE Exam Simulator to open VCE files

HOW TO OPEN VCEX FILES
Use ProfExam Simulator to open VCEX files


ProfExam at a 20% markdown
You have the opportunity to purchase ProfExam at a 20% reduced price
Get Now!



